Data Breach: Strategic Investigation, Response, & Recovery
We specialize in providing data breach remediation services to companies in Austin, TX, Our expert data breach consultants can help you mitigate a data breach by addressing any damage done and helping you prevent it from happening again.
Responding to a data breach requires experts who know how to identify and mitigate an immediate threat, investigate underlying vulnerabilities that led to the data breach, address any regulatory compliance implications, and restore order right away. With its own, fully-staffed, 24x7x365 Security Operations Center, TRUE has the highly trained security analysts, advanced tool sets, security clearance levels, and years of expertise to provide a fully coordinated data breach response team to restore order during what can feel like a chaotic event for any organization. If you are looking for a top data breach services company in Austin, look no further.

Restore & Rebuild
RIGHT AWAY, OUR EXPERTS WILL
- Contain the data breach
- Prevent further exfiltration of data
- Make sure attackers are out of your systems
- Preserve any digital forensics evidence to assist with investigation
Remember, this is a potential crime scene. Don’t touch anything.

Learn how one company recovered from total ransomware shutdown, and prevent this from happening to your organization.
DOWNLOAD CASE STUDYOur experts will immediately work to understand your situation and infrastructure, what assets need immediate protection, and how your incident has come to light. For all known threats, we will help you stop the attack and secure affected systems right away. At the same time, TRUE security professionals will deploy short-term, 24/7/365 monitoring tools to watch your network and endpoints, giving our round-the-clock security analysts the ability to immediately intervene and respond to any additional areas of your systems to which the attack may have spread. From there, forensics can be performed to determine the origin and cause, helping you isolate what vulnerabilities may have been exploited and all traceable information about who, what, when, where, and how the data breach has occurred.
When your systems have been secured, TRUE’s experts will give you options on how you can restore your environment to working order as efficiently as possible. Our TrueIT Teams will be available to work as an extension of your existing team to help restore and rebuild any affected systems needing additional remediation, enabling you to keep your business running and minimize any downtime your operations may have experienced from the attack. You may have a full internal IT team, in which case we can explain next steps and support you with insight as needed. If you need to supplement your team, however, TRUE maintains a deep bench of specialists who can assist with everything from Microsoft configurations, to firewalls, to cloud deployments, to custom engineered solutions, and everything in-between.
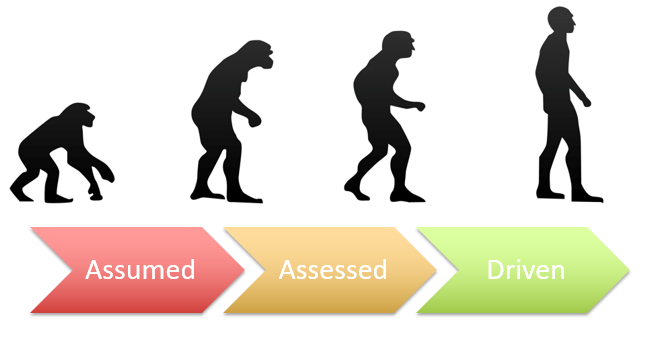
One of the most important steps post-breach is to examine your systems and organizational approach to security for ways to prevent the same thing–or worse– from happening in the future. TRUE supports your efforts with end-to-end services to maximize the efficiency of your internal IT teams. Our Vulnerability Management Program proactively identifies and remediates vulnerabilities in your systems before they become an avenue for attack, with automated scans backed by expert security analysts, unified threat feeds, and ongoing security consultation to help you prioritize and plan remediation efforts. For threats at the endpoint level, TRUE offers Managed Detection and Response (MDR), also backed by the security experts in our 24/7/365 Security Operations Center. TRUE’s IT specialists and engineers are also available to help you patch, manage, air gap, configure, deploy, or harden whatever parts of your environment need additional support. Finally, our Security Consultants are here to help you improve, maintain, test, and validate your overall security posture, growing a program that will support and protect your business goals.
TRUE’s bench includes experts across disciplines. Whether you need help complying with breach notification laws, someone to work hand-in-hand with inside and outside counsel, keeping them informed of progress throughout and after the Incident Response engagement, or an objective security expert who knows how to navigate the nuances of working with your cybersecurity insurance provider, TRUE has you covered. Our internal experts and extensive network of partners will help you address corporate issues that may arise in the event of a security incident.

- TRUE Digital Forensics and Incident Response (DFIR) Services can help you address a data breach NOW.
- • Investigate, Contain, & Recover
- • Identify Impacted Systems
- • Analyze & Mitigate Threats
- • Assess Damage
- • Assist with Regulatory Compliance Requirements
- • Deploy Emergency Sensor to ensure threat is not ongoing
- • Assist with Cyber Insurance and Legal issues
- • Prevent Incident Recurrence
- • Help with Notifications
- • Provide Executive Summary with Plan for Future Prevention
- • Support Policy Development
Get Started with True Digital Security
Start Protecting Your Business’s Data with Digital Security Preparedness. Whether you are ready to be proactive, with a Security Incident Response Plan, need immediate remediation support to stop an attack now, or want to initiate a forensics investigation into a past event, TRUE is your IR partner. Organizations of every size and in nearly every industry rely on TRUE to protect their sensitive data in an emergency, including regulated industries such as Health Tech, Payment Tech, Health Care, Financial Services, and more. TRUE is ready to deploy immediately in your time of need.
Contact Us Today!
Let us know your business needs and we will make sure to get back with you promptly!
Contact Information
-
HEADQUARTERS
6900 E. Camelback Rd., Suite 900
Scottsdale, AZ 85251 -
Oklahoma Office
1350 South Boulder Avenue, Suite 1100
Tulsa, OK 74119 -
Region Metropolitana
Chile - 480-389-3444